Modern businesses depend on third-party apps for everything from customer service and analytics to...
Suspicious Emails - Is your Account Compromised?
You just received an email from your escrow officer. It has the wiring instructions to close on your new home. Conveniently missing from the message is the big bold text reminding you that wire instructions are never sent via email and should always be confirmed via phone. Even if you did call, the phone number in the signature is slightly different than the number you would normally call.
But everything else looks correct, including the formatting of the signature and warnings and disclaimers.
It must be safe to wire your hard-earned money following these instructions, right? After all, you’re expecting this email. Who else could know you’re even buying a house?
Somewhere along the line, some did learn though.
And they intercepted an email from the escrow officer.
They deleted it from your inbox before you even got that ding on your iPhone.
Then they replaced it with their fraudulent email.
Before sending any funds, call using prior information or publicly accessible information to confirm the validity of any emails, especially financial ones.
How to tell if your account was compromised
Just because you’re on the receiving end doesn’t mean it was the sender. Fraudsters will try to access every link they can. If they can access your account, they can setup rules to delete/hide/forward the legitimate email as well as any emails you might send to the legitimate address. Then they intercept those messages and replace them with their fraudulent messages.
Review your sign in logs.
For Microsoft: https://mysignins.microsoft.com/
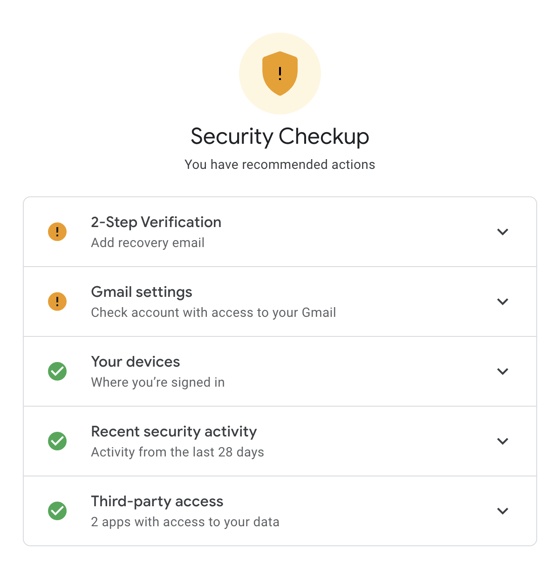
For Google: https://myaccount.google.com/security-checkup/4
Look at the activity for anything that doesn’t look like you. Click the Look unfamiliar? Secure your account link or See unfamiliar activity button.
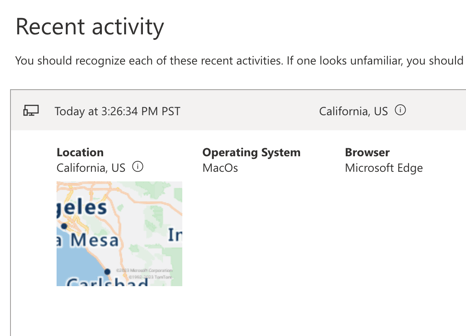
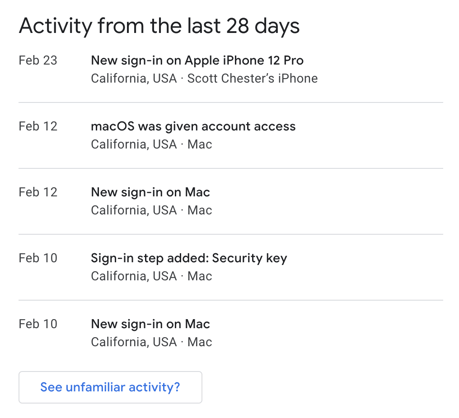
Note: If you see failures in your sign in logs, that means that someone tried to access your account, but was not successful. Pay extra attention though, as this indicates that you are actively being targeted and you need to be extra vigilant!
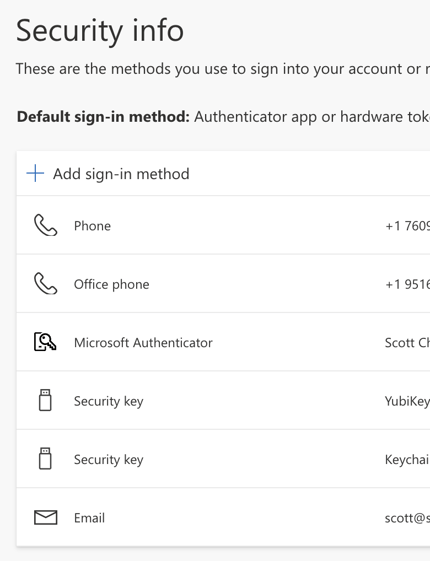
Review security info
For Microsoft: https://mysignins.microsoft.com/security-info
For Google: https://myaccount.google.com/security-checkup/1
If you don’t already have MFA (2-Step) enabled, enable it now. MFA isn’t perfect, but without a second factor, attackers will easily get into your account. Passwords are not enough.
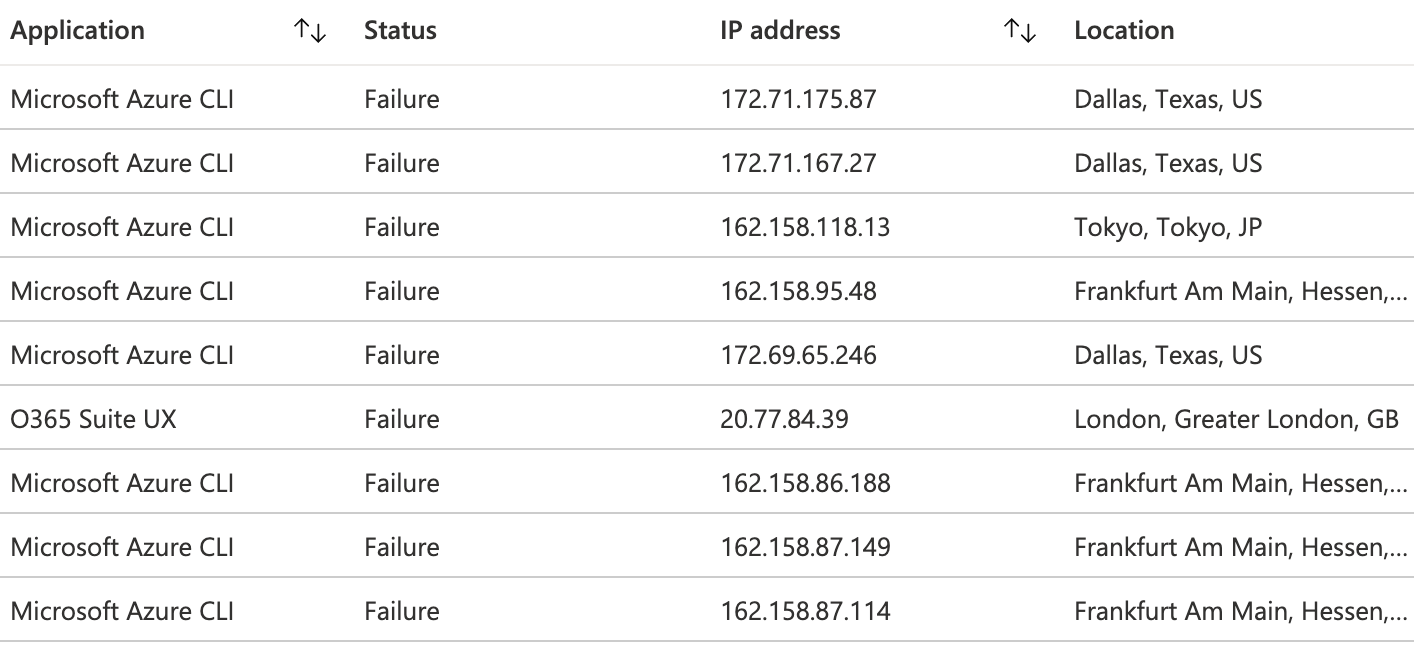
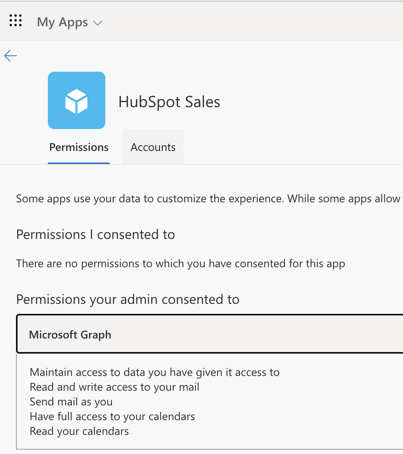
Review any approved applications
For Microsoft: https://myapps.microsoft.com/
For Google: https://myaccount.google.com/security-checkup/3
As we’ve made it harder for attackers to get into accounts with MFA, they’ve started creating fake applications to gain persistent access to your mailbox. Remove any apps you don’t recognize/use. Note that in Microsoft, you can click the dots and then manage your application to review what permissions it is granted. If you’ve ever used sign in with Microsoft account on a website instead of creating a password, you’ll likely see that application listed here with view your basic profile/email address permissions. You’re really looking for any app that has permission to access your mail.
Review any mail forwarding rules
For Microsoft: https://outlook.office.com/mail/options/mail/rules
For Google: https://mail.google.com/mail/#settings/filters
Some people use these rules to move mail to folders or similar. Others have no idea what they are. If you don’t know, you shouldn’t see any rules there. Be especially cautious of any rule that is deleting or forwarding mail.
Review any forwarding rules
For Microsoft: https://outlook.office.com/mail/options/mail/forwarding
For Google: https://mail.google.com/mail/#settings/fwdandpop
Unless you’ve set this up yourself, it is unlikely that you are forwarding mail anywhere legitimately.
Review your sent items
While not perfect, as someone who had access to your account could have deleted any sent items, check there to see if you see anything that you didn’t send.
Your mail administrator may have access to back-end mail logs to show any mail sent and removed from your mailbox.
Change your password
If it has been a while since you changed their password, or if you currently use an insecure password, you may want to consider changing your password even if there are no indicators of compromise. Likewise, if you use that same password anywhere else, change it to something unique at each service. This helps prevent a compromised account at one service from impacting other services.
If you want to see how many times your accounts have been publicly compromised, check https://haveibeenpwned.com/ and you'll probably find your email address has been exposed somewhere (unlikely related to the current incident).
You can even put in some of your favorite passwords at https://haveibeenpwned.com/Passwords to see if that password has been exposed somewhere.
Finally, since everyone loves AI, here’s some advice from ChatGPT:
If you suspect that your email has been compromised, you should take immediate action to secure your account and protect your personal information. Here are some steps you can take:
Change your password: The first step is to change your email password immediately. Choose a strong, unique password that is not used for any other accounts.
Enable two-factor authentication: Enable two-factor authentication (2FA) for your email account, which provides an extra layer of security. With 2FA, you'll need to enter a verification code in addition to your password to log in.
Check your account settings: Check your email account settings to make sure that no one has made any unauthorized changes to your account, such as forwarding your emails to another address.
Scan your computer for malware: Scan your computer for malware and viruses, which can be used to steal your personal information.
Review your email activity: Review your email activity to check for any suspicious activity, such as emails you didn't send or messages that have been marked as read but you didn't open.
Contact your email provider: If you suspect that your email has been compromised, contact your email provider immediately for further assistance.
Change your password for other accounts: If you use the same password for other accounts, change those passwords as well to ensure that your other accounts are not compromised.
Remember to be cautious when using public Wi-Fi or any other unsecured network as this can be a way for hackers to gain access to your email account.
When it doubt, check with your IT provider.


.jpg?height=200&name=marvin-meyer-SYTO3xs06fU-unsplash%20(1).jpg)